Tips: Secure Your Wireless Connection with WPA/WPA2 Encryption
If you have your own wireless internet connection, it might be unsecured (meaning that you don’t have to type in a password to access it) or it may be using WEP encryption. There are several important reasons why you should encrypt your internet (or switch from WEP encryption to a stronger method such as WPA or WPA2):
Leaving your wireless internet unsecured lets anybody access your network which can cause slow connection speeds.
If an intruder illegally downloads something using your wireless internet, you could be legally liable for their actions.
An intruder could potentially monitor your network traffic and obtain passwords or other confidential information.
WEP encryption can be easily cracked in a matter of minutes, which makes it only slightly better than an unsecured connection.
This guide will show you how to identify the current security used on your wireless network, and how to better secure it with WPA / WPA2 encryption.
Identifying Your Current Security Mode
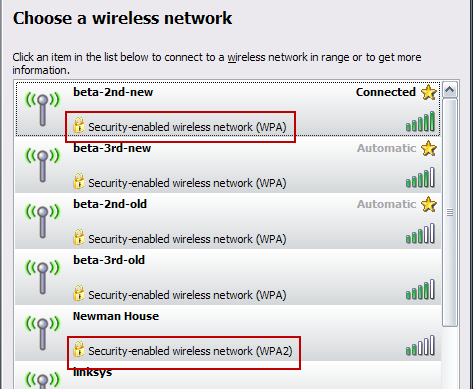
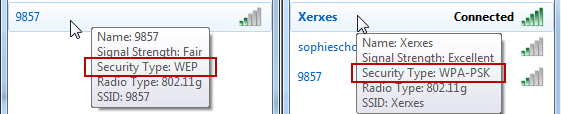
Most of the time, you can see what type of security an access point uses before connecting to it. View your available wireless networks and check out your own network to see what your current security settings are.
If you see WPA or WPA2 next to your connection – that’s great, you’re done. WPA and WPA2 provide strong protection as long as you use a good password. When creating a password, avoid using dictionary words and try to include complex characters like !@#$%^&*.
If you see WEP or no security, it’s time to add WPA or WPA2 to your access point.
Enabling WPA/WPA2
Wireless security options are different for every access point and router, so refer to your user’s manual or check out the device manufacturer’s support information online. Your device may even come with an installation disc that can walk you through security setup.
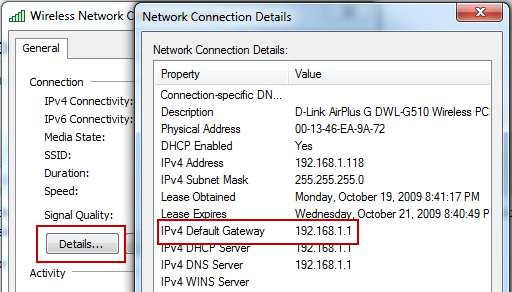
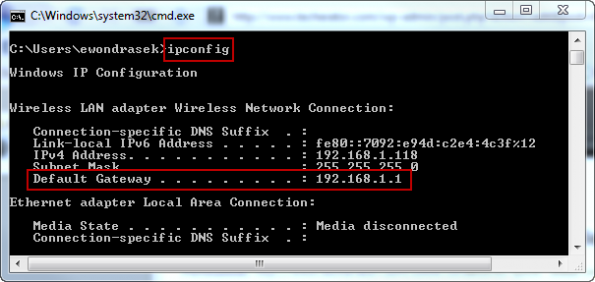
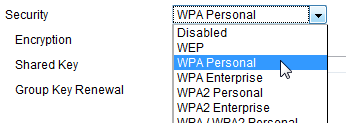
In general, you need to locate a Wireless/Wireless Security section in your access point’s configuration and enable WPA or WPA2 security. With many access points and routers, you can type in the Gateway address of your internet connection in a web browser to access the device’s configuration page.
Note: The Gateway address can be found by viewing your current connection’s details (varies by your operating system) or by pressing Windows Key + R, type cmd and press enter, then type ipconfig and press enter.
In my case, my router’s address is 192.168.1.1, so I typed that address in my browser and pressed enter. This will open the device’s configuration page (you may need to enter login credentials to access this page). Locate a Wireless Security section (this may be under Wireless, look around until you find it) and enable WPA or WPA2 security, selecting ‘Personal’ if it gives you the option. Create a strong password and click save. You will have to re-join your network once this has been done.
Now that you’ve enabled security on your wireless connection, it will be much more difficult for an intruder to steal your internet access or perhaps obtain confidential information.
Have any tips for better securing your internet connection? Share them with us in the comments.
From: Techerator!
Leaving your wireless internet unsecured lets anybody access your network which can cause slow connection speeds.
If an intruder illegally downloads something using your wireless internet, you could be legally liable for their actions.
An intruder could potentially monitor your network traffic and obtain passwords or other confidential information.
WEP encryption can be easily cracked in a matter of minutes, which makes it only slightly better than an unsecured connection.
This guide will show you how to identify the current security used on your wireless network, and how to better secure it with WPA / WPA2 encryption.
Identifying Your Current Security Mode
Most of the time, you can see what type of security an access point uses before connecting to it. View your available wireless networks and check out your own network to see what your current security settings are.
If you see WPA or WPA2 next to your connection – that’s great, you’re done. WPA and WPA2 provide strong protection as long as you use a good password. When creating a password, avoid using dictionary words and try to include complex characters like !@#$%^&*.
If you see WEP or no security, it’s time to add WPA or WPA2 to your access point.
Enabling WPA/WPA2
Wireless security options are different for every access point and router, so refer to your user’s manual or check out the device manufacturer’s support information online. Your device may even come with an installation disc that can walk you through security setup.
In general, you need to locate a Wireless/Wireless Security section in your access point’s configuration and enable WPA or WPA2 security. With many access points and routers, you can type in the Gateway address of your internet connection in a web browser to access the device’s configuration page.
Note: The Gateway address can be found by viewing your current connection’s details (varies by your operating system) or by pressing Windows Key + R, type cmd and press enter, then type ipconfig and press enter.
In my case, my router’s address is 192.168.1.1, so I typed that address in my browser and pressed enter. This will open the device’s configuration page (you may need to enter login credentials to access this page). Locate a Wireless Security section (this may be under Wireless, look around until you find it) and enable WPA or WPA2 security, selecting ‘Personal’ if it gives you the option. Create a strong password and click save. You will have to re-join your network once this has been done.
Have any tips for better securing your internet connection? Share them with us in the comments.
From: Techerator!
Implement switch security on your network
Takeaway: Switch security involves challenges. Take a look at how you can ensure switch security in your organization.
When it comes to securing internal networks, one area that organizations often overlook is switch security. Most companies tend to focus on their borders and end users, forgetting the devices that connect the two.
Ensuring switch security in your organization basically comes down to two steps: Defining what users can see, and defining what they can connect.
What you see
Every business-grade switch allows you to define virtual local area networks (VLANs). Organizations typically implement VLANs for the following reasons:
Broadcasts: A VLAN doesn't pass broadcast traffic to nodes that aren't part of the VLAN.
Performance: A VLAN can reduce the number of router hops and extend your local topology between user workstations and resource servers, increasing the apparent bandwidth for network users.
Departments: A VLAN can segment departments that use bandwidth-intense applications. You can also dedicate a VLAN to specific types of job roles (e.g., executives, kiosk workstations, etc.).
Security: A VLAN allows organizations to separate sensitive clusters of systems from the rest of the network, decreasing the likelihood that users will gain access to information on these clients and servers.
What you connect
Port security is also available on every business-class switch. Some switches allow very in-depth settings; others just provide some of the basics. Here's a look at some of your options:
MAC Locking: This involves tying a Media Access Control (MAC) address of one or more connected devices to a physical port on a switch. If you lock a switch port to a particular MAC address, you don't have to worry about superusers or internal black hats creating backdoors into your network with rogue access points.
MAC Lockout: This disables a specified MAC address from ever connecting to a switch.
MAC Learning: Using knowledge about each switch port's direct connections, the switch can set security based on current connections.
Remote Configuration: Limit remote configuration to specific IP addresses, using SSH instead of Telnet. Telnet passes usernames and passwords in clear text, potentially allowing everyone on the LAN segment to see login credentials.
Final thoughts
Switch security does involve challenges, particularly when it comes to setting up and deploying new workstations in your help desk area. This is definitely an issue you should consider when implementing a switch security policy.
Network administrators who balk at port security because it's labor-intensive and requires constant management should consider this: Port security stops people from attaching wireless access points and bypassing your site security. That alone should be a good enough reason to implement switch security on your network today.
By Michael
When it comes to securing internal networks, one area that organizations often overlook is switch security. Most companies tend to focus on their borders and end users, forgetting the devices that connect the two.
Ensuring switch security in your organization basically comes down to two steps: Defining what users can see, and defining what they can connect.
What you see
Every business-grade switch allows you to define virtual local area networks (VLANs). Organizations typically implement VLANs for the following reasons:
Broadcasts: A VLAN doesn't pass broadcast traffic to nodes that aren't part of the VLAN.
Performance: A VLAN can reduce the number of router hops and extend your local topology between user workstations and resource servers, increasing the apparent bandwidth for network users.
Departments: A VLAN can segment departments that use bandwidth-intense applications. You can also dedicate a VLAN to specific types of job roles (e.g., executives, kiosk workstations, etc.).
Security: A VLAN allows organizations to separate sensitive clusters of systems from the rest of the network, decreasing the likelihood that users will gain access to information on these clients and servers.
What you connect
Port security is also available on every business-class switch. Some switches allow very in-depth settings; others just provide some of the basics. Here's a look at some of your options:
MAC Locking: This involves tying a Media Access Control (MAC) address of one or more connected devices to a physical port on a switch. If you lock a switch port to a particular MAC address, you don't have to worry about superusers or internal black hats creating backdoors into your network with rogue access points.
MAC Lockout: This disables a specified MAC address from ever connecting to a switch.
MAC Learning: Using knowledge about each switch port's direct connections, the switch can set security based on current connections.
Remote Configuration: Limit remote configuration to specific IP addresses, using SSH instead of Telnet. Telnet passes usernames and passwords in clear text, potentially allowing everyone on the LAN segment to see login credentials.
Final thoughts
Switch security does involve challenges, particularly when it comes to setting up and deploying new workstations in your help desk area. This is definitely an issue you should consider when implementing a switch security policy.
Network administrators who balk at port security because it's labor-intensive and requires constant management should consider this: Port security stops people from attaching wireless access points and bypassing your site security. That alone should be a good enough reason to implement switch security on your network today.
By Michael